What is Oursurfing.com? Is it safe?
Oursurfing.com is classified as a browser hijacker which is able to modify your homepage and default settings of browsers such as Internet Explorer, Google Chrome and Mozilla Firefox. If your computer is infected with the browser hijacker, every time you open your browser or a new tab, you will be always redirected to http://oursurfing.com/. It can use a variety of Registry entries to hijack your browsers even after you clean your shortcuts or change your home page settings. It is really hard to deal with, thus, you should find effective way to remove it as soon as you can.
The screenshot of Oursurfing.com:
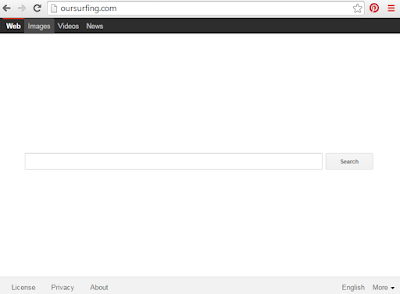
Once the Oursurfing.com successfully installed on your computer, it will become a big threat which may not only decline entire computer performance. Not only can it modify your default homepage, but also redirect you to other sites. In other words, if you try to search something by using this fake search engine, it only gives you non-sense and irrelevant results. So you will find that your web pages which can be full of ads, links, and banners. Some of these ads or links might contain different kinds of malware/viruses and clicking on them may lead to more malware/viruses infections. In addition, your registry settings and other important windows will be changed. Thus, the infected system of computer becomes more and more vulnerable. And other harmful computer threats will get the chance to enter into your computer. As a result, you computer performs slowly and poorly because it has occupied lots of system resource. What's worse, this Oursurfing.com is able to keep track of your surfing habits. This means that it will steal your personal information.
How to remove Oursurfing.com from Your PC?
Method one: Manually remove Oursurfing.com from your system.
Method two: Remove Oursurfing.com Permanently with Spyhunter Antivirus software.
Manual steps:
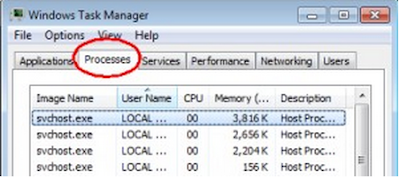
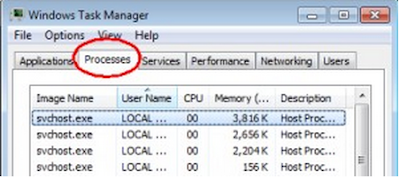
Step 1: End all the processes related to Oursurfing.com from task manager.
Open task manager by pressing Alt+Ctrl+Del keys at the same time or type taskmgr into the search blank. Then, press OK. Stop all the running processes of Oursurfing.com.
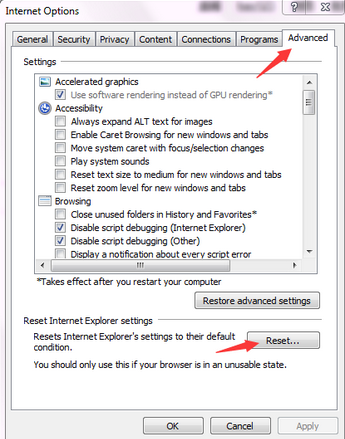
Internet Explorer
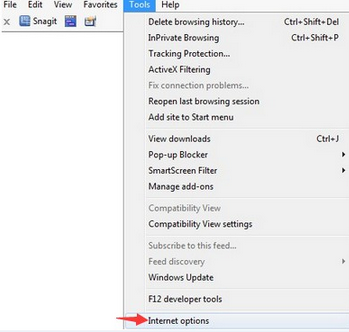
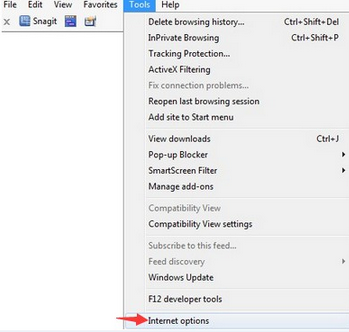
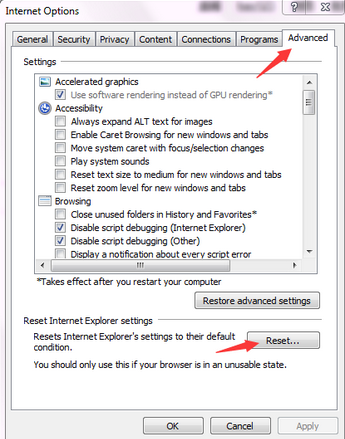
(1) Open Internet Explorer, choose Tools menu and then select Internet Options.
(2) Choose Advanced tab in the Internet Options window, and then click on Reset button
(4) Click OK.
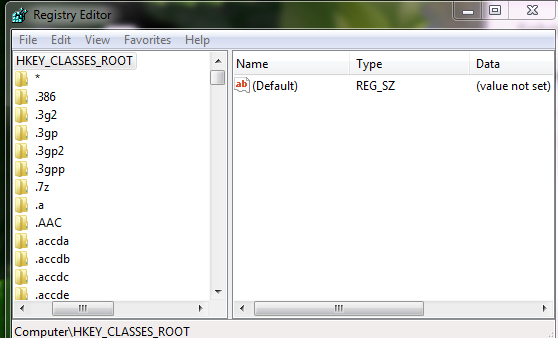
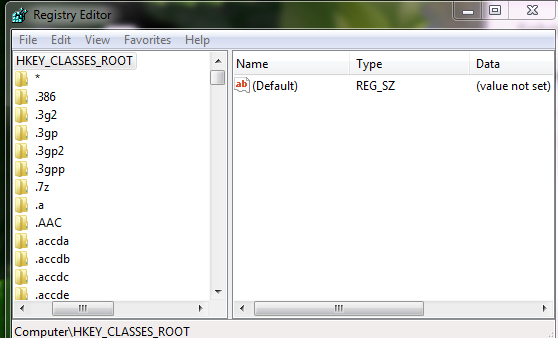
Step 3: Remove Oursurfing.com from Registry Editor.
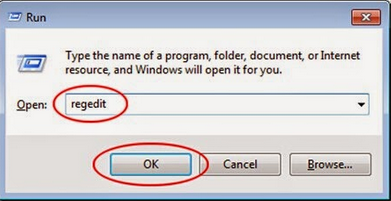
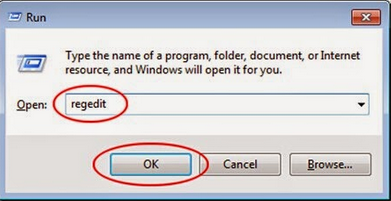
(1) Go to Start Menu and open Registry Editor.
(2) In the opened Window, type in Regedit and then click OK.
(3) Remove the related files and registry entries in Registry Editor.
What can SpyHunter do for you?
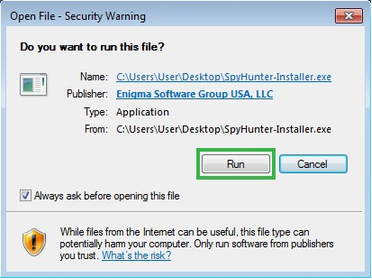
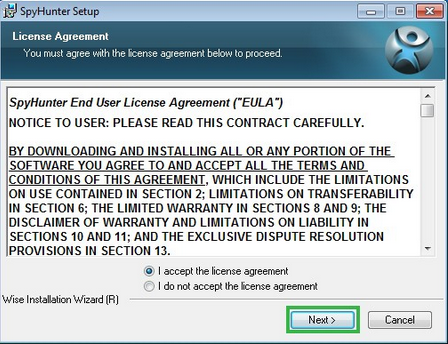
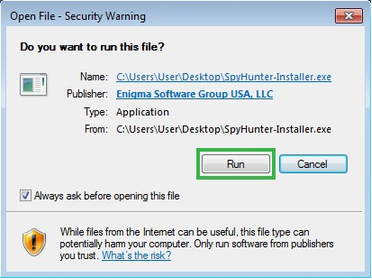
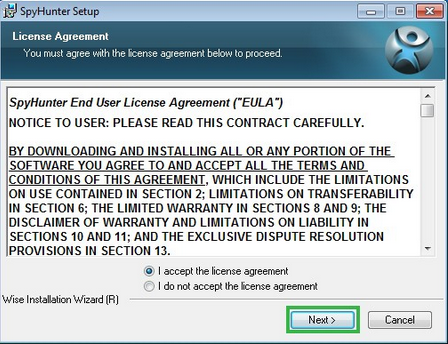
Step one: Click the icon to download SpyHunter removal tool

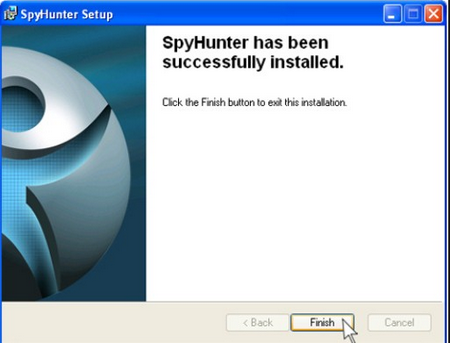
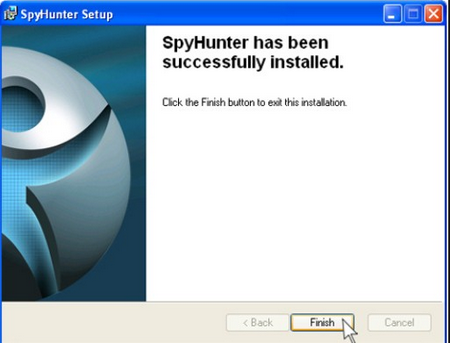
Follow the instrutions to install SpyHunter removal tool.
Step two: After the installation, run SpyHunter and click “Malware Scan” button to have a full or quick scan on your PC.
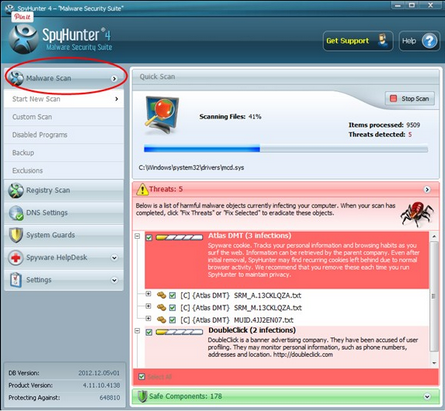
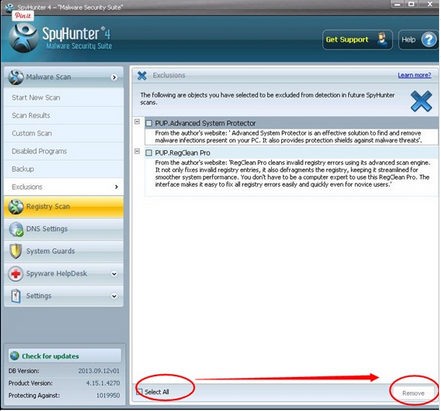
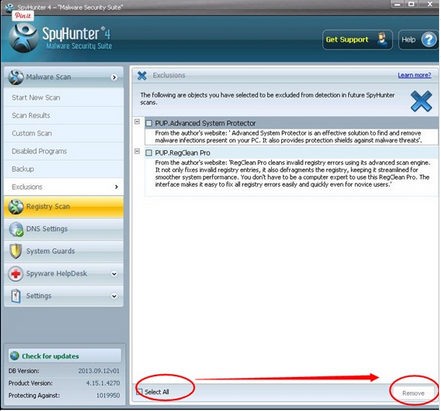
Step three: Select the detected malicious files after your scanning and click “Remove” button.
Optimizing Your System After Threat Removal (Optional)
(1) Go to Start Menu and open Registry Editor.
(2) In the opened Window, type in Regedit and then click OK.
(3) Remove the related files and registry entries in Registry Editor.
Automatic steps - by use of SpyHunter
- Give your PC intuitive real-time protection.
- Detect, remove and block spyware, rootkits, adware, keyloggers, cookies, trojans, worms and other types of malware.
- Spyware HelpDesk generates free custom malware fixes specific to your PC.
- Allow you to restore backed up objects.
Step one: Click the icon to download SpyHunter removal tool

Follow the instrutions to install SpyHunter removal tool.
Step two: After the installation, run SpyHunter and click “Malware Scan” button to have a full or quick scan on your PC.
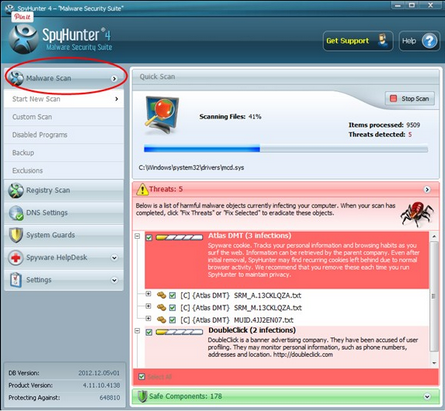
Step three: Select the detected malicious files after your scanning and click “Remove” button.
Optimizing Your System After Threat Removal (Optional)
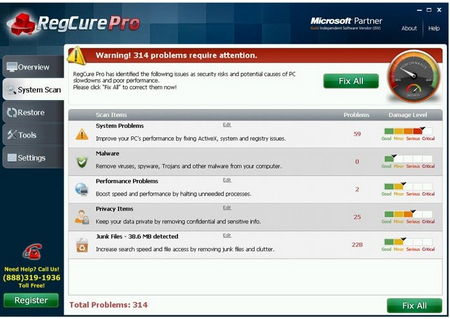
What can RegCure Pro do for you?
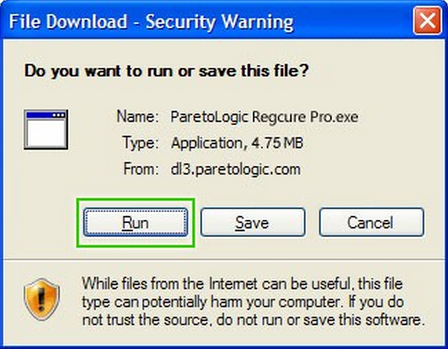
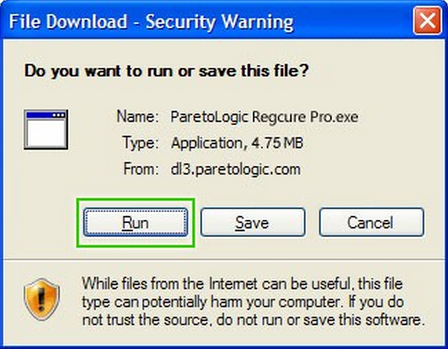
Step 1. Download PC cleaner RegCure Pro
a) Click the icon below to download RegCure Pro automatically

b) Follow the instructions to finish RegCure Pro installation process

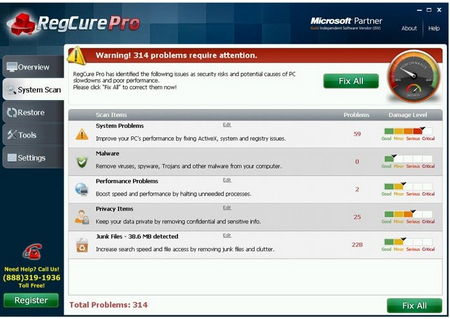
Step 2. Run RegCure Pro and start a System Scan on your PC.

Step 3. Use the in-built “Fix All" scheduler to automate the whole optimization process.
After using these methods, your computer should be free of Oursurfing.com. If you do not have much experience to remove it manually, it is suggested that you should download the most popular antivirus program SpyHunter to help you quickly and automatically remove all possible infections from your computer.
- Fix system errors.
- Remove malware.
- Improve startup.
- Defrag memory.
- Clean up your PC.
Step 1. Download PC cleaner RegCure Pro
a) Click the icon below to download RegCure Pro automatically

b) Follow the instructions to finish RegCure Pro installation process

Step 2. Run RegCure Pro and start a System Scan on your PC.

Step 3. Use the in-built “Fix All" scheduler to automate the whole optimization process.

No comments:
Post a Comment